Today, we’re going to dive into an attack tactic that, despite its simplicity and reliance on social engineering, has proven incredibly effective at bypassing defenses and achieving remote code execution (RCE): ClickFix.
Popularized by researchers like John Hammond and documented in the ClickGrab project, ClickFix is a stark reminder that “layer 8” (the user) remains the most vulnerable point in any security architecture.
What Is ClickFix and How Does It Work?
In essence, ClickFix is a social engineering technique that exploits the user’s trust and lack of knowledge about how system shortcuts and the clipboard work.

The process is divided into precise steps:
1. Clipboard Poisoning (Client-Side):
- An attacker creates a malicious web page.
- When visited, this page executes a JavaScript script (usually
navigator.clipboard.writeText()) that silently overwrites the user’s clipboard content with a malicious command.
This happens without any explicit user interaction in most modern browsers in “user-initiated event” contexts or even in some cases without a direct event if the security policy allows it (which is becoming more restricted, but still possible in specific scenarios).
2. Social Engineering and Execution Inducement:
- The page displays misleading instructions to the user, with messages like “verify your session,” “fix a system error,” “update a driver,” or “confirm your identity.”
- The instructions ask the user to perform a key sequence:
Windows + R(on Windows) orAlt + F2(on GNOME/Linux): This shortcut opens the “Run” dialog box, a powerful tool that accepts and executes commands directly on the operating system.Ctrl + V(Paste): The user, innocently, pastes the “verification code” into the “Run” box. However, what is pasted is the malicious command that was inserted into the clipboard.Enter: By pressing Enter, the user AUTHORIZES the execution of the malicious command.
3. Payload Execution:
- The command can be anything the attacker desires: from a simple command like
calc.exe(as we use in our labs for harmless PoCs) to complex payloads like PowerShell scripts,curl | bashcommands on Linux systems, or even calls to LOLbins (Living Off the Land Binaries) for downloading and executing binaries.
Why is ClickFix So Dangerous for Cybersecurity and Networks?
The simplicity of ClickFix hides its lethality, especially for security teams:
- Bypassing Perimeter Defenses: The attack does not rely on software vulnerability exploits in the browser or system. It tricks the user into executing the command, bypassing WAFs, IDS/IPS, and many email protections.
- Endpoint Detection Challenge (EDR): The execution process is initiated by the user themselves through a legitimate system binary (like
explorer.exeon Windows, which launches the “Run” box). This can make detection based on process patterns or anomalies difficult, requiring more sophisticated EDR rules that analyze the full command line and context. - Cross-Platform: As we demonstrated in the lab, the technique works equally well on Windows and Linux (and theoretically on macOS with the equivalent shortcut for a run prompt). The platform-agnostic nature of social engineering is a major challenge.
- Short Attack Chain: RCE is achieved with very little interaction and in a matter of seconds, leaving little time for the user or security systems to react.
How to Protect Your Users and Network from ClickFix?
Defending against ClickFix requires a layered approach that combines education, endpoint hardening, and network monitoring:
- User Awareness (The First Line of Defense):
- “The Notepad Rule”: Teach users to ALWAYS paste suspicious content into a plain text editor (like Notepad) BEFORE executing it or pasting it into any command window. This reveals the actual payload.
- Shortcut Education: Train users to be wary of any request from a website to use system shortcuts like
Win+RorAlt+F2. Legitimate sites rarely require this. - Principle of Distrust: Reinforce that if something seems too easy or too urgent, it should be treated with suspicion.
- Endpoint Hardening (Security Posture):
- Principle of Least Privilege: Ensure users operate with minimum privilege accounts. This significantly limits the impact of a payload even if it is executed.
- GPO/MDM (Windows): In corporate environments, consider disabling access to the “Run” box (
Win+R) for standard users via GPOs (Group Policy Objects) or MDM solutions. - Application Control (AppLocker, WDAC, AppArmor): Implement application control policies that restrict the execution of unauthorized binaries and scripts. This can block the payload’s execution even if the user pastes it.
- PowerShell/Scripting Restriction: Configure policies for PowerShell or other script interpreters to disable the execution of unsigned scripts or restrict functionality.
- Monitoring and Detection (Detection Security):
- Advanced EDR/XDR: Invest in EDR/XDR solutions that have advanced capabilities for detecting command-line anomalies and process telemetry. Custom rules can be created to alert on executions of PowerShell,
curl,wget, orbashwith suspicious parameters when originating from processes likeexplorer.exeor from unexpected contexts. - Network Monitoring: Although the initial attack is on the endpoint, the payload will often try to communicate with a C2 (Command and Control) server via HTTP/HTTPS. Monitor network traffic to detect these anomalous connections, especially to newly registered domains or unusual IPs.
- SIEM and Correlation: Correlate EDR and network logs to identify the full attack chain, from web browsing to post-exploitation activity.
- Advanced EDR/XDR: Invest in EDR/XDR solutions that have advanced capabilities for detecting command-line anomalies and process telemetry. Custom rules can be created to alert on executions of PowerShell,
Conclusion
ClickFix is a vivid reminder that the attack surface extends far beyond source code and devices. It encompasses human cognition and the way we interact with technology.
For cybersecurity and networking professionals, this means our strategies must be holistic, combining the latest technology with fundamental user education.
Prevention is always the best defense, but the ability to detect and respond quickly is equally crucial.
Have you ever encountered ClickFix in your scans or audits? What strategies does your team use to mitigate this type of attack? Share your experiences and insights in the comments below!
See more:
UFW Limit: The Smart Defense Against Brute-Force Attacks
How to Scan for Rootkits and Malware on Linux Servers with chkrootkit
AIDE : IDS for Linux Ubuntu Installation and Configuration
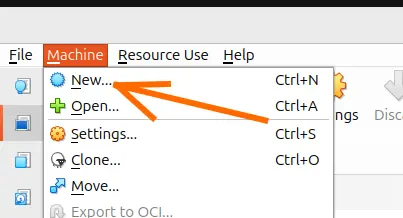
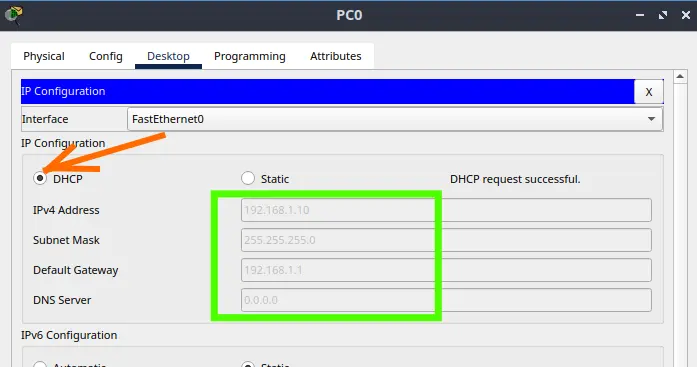
Why use Kali Linux inside VirtualBox?
How to Install Kali Linux on VirtualBox: Step-by-Step Guide for Beginners

Juliana Mascarenhas
Data Scientist and Master in Computer Modeling by LNCC.
Computer Engineer