Kali Linux is the standard Swiss Army knife for any cybersecurity professional. Its repository is vast, but here’s an inconvenient truth: not all tools are created equal.
Many of them, although historically important, are now obsolete, noisy, or have simply been surpassed by much faster and more efficient alternatives.
Using obsolete tools isn’t just inefficient; it’s a risk. You might be running the wrong tests and wasting precious time that could be spent learning more and increasing the security of the assets you are protecting.
As an expert in the field, I see many beginners falling into the trap of old tutorials. Let’s retire some tools and modernize your arsenal.
1. Network Attacks (MITM): Goodbye Ettercap, Hello bettercap
The Problem: Ettercap and dsniff
Ettercap was the king of Man-in-the-Middle (MITM) for over a decade. However, anyone who has used it in a modern network environment knows that it is unstable, prone to crashes, and its plugins are outdated.

The Modern Replacement: bettercap
bettercap is what Ettercap should have become. Written in Go, it is incredibly fast, stable, and modular.
Why is bettercap superior?
- Stability: It almost never crashes.
- Modularity: It has “caplets” (scripts) that automate complex attacks.
- All-in-One: It performs ARP spoofing, DNS spoofing, network sniffing, HTTP(S) proxying, and can even decrypt SSL/TLS traffic with semi-automated HSTS bypass.
2. Web Fuzzing: Swap wfuzz for ffuf
The Problem: wfuzz
Don’t get me wrong, wfuzz still works. It’s a solid tool written in Python. But in the world of bug bounty and web pentesting, speed is everything. And Python, in this regard, loses badly.

The Modern Replacement: ffuf (Fuzz Faster U Fool)
Written in Go, ffuf is the new gold standard for web fuzzing for one simple reason: absurd speed. It is designed to be massively concurrent (use multiple threads) and can perform thousands of requests per second.
Why is ffuf superior?
- Speed: It is dramatically faster than any Python-based tool.
- Simplicity: The command-line syntax is clean and intuitive.
- Filtering: It has extremely powerful and easy-to-use filter and matcher options.
3. Post-Exploitation (C2): The End of (PowerShell) Empire
The Problem: PowerShell Empire
Empire was revolutionary. It showed the world the power of PowerShell for post-exploitation. The problem? The world noticed.
Today, PowerShell is one of the most monitored surfaces in any Windows environment. AMSI (Antimalware Scan Interface), Script Block Logging, and other protections have made the classic Empire “noisy” and easy to detect.
The Modern Replacements: Sliver, Covenant, or Havoc
The game has changed from PowerShell to C# and other languages.
- Sliver: A modern C2 framework, written in Go, focused on evasion and flexibility. It is the current favorite of many red teams.
- Covenant: A C2 written in .NET Core, making it a natural choice for Windows environments.
- Havoc: A newer C2 focused on being modular and evasive against modern EDRs.
4. Password Cracking: The Death of Ophcrack
The Problem: Ophcrack
Ophcrack was a magical tool that used rainbow tables to crack Windows password hashes (LM/NTLM) in seconds.
The problem is that rainbow tables are useless against modern passwords that use “salting,” and LM hashes have not been used since Windows Vista.
The Modern Replacements: Hashcat and John the Ripper (JTR)
This isn’t even a “replacement”; it’s the industry standard. Instead of relying on pre-computed tables, the power is now in your GPU.
- Hashcat: The world’s fastest password cracker. It uses the power of your graphics card (GPU) to try billions of passwords per second.
- John the Ripper: The classic that still works perfectly, great for CPU and very flexible.
5. GUI for Exploitation: Retire Armitage
The Problem: Armitage
Armitage was a popular graphical user interface (GUI) for Metasploit. The idea was to “facilitate” cybersecurity testing.
The problem is that it is slow, limited, and, most importantly, it prevents you from learning how to use the most powerful tool that exists: the command line.
The Modern Replacement: msfconsole (and Pwntools)
A pentest professional does not click buttons to exploit a flaw.
- msfconsole: The Metasploit command-line interface is infinitely faster, more powerful, and more flexible. Learning to use
msfconsolecorrectly (with itsset,exploit,use, and routing commands) is mandatory. - Pwntools: For those who investigate exploits (especially in binary exploitation), this Python library is the essential tool.
Conclusion: Why Keeping Your Arsenal Updated is Crucial?
In cybersecurity, the “toolbox” is not static. Defense evolves, and cybersecurity professionals must evolve with it.
Keeping up-to-date with the most modern tools is not just a matter of preference; it is a professional necessity.
Modern tools are, in general:
- Faster: Written in compiled languages like Go or Rust.
- More Evasive: Built with detection (EDR, AV) in mind.
- More Stable: Fewer bugs and crashes during an engagement.
Don’t get stuck in the past. Test, update, and optimize your arsenal.
Ethical Use Warning: All tools and techniques discussed in this article are for educational and security purposes. They must be used responsibly, only in controlled test environments or with explicit authorization from the system owner. Ethical use is what differentiates a security professional from an attacker.
See more:
Maverick Malware: Why the WhatsApp (.ZIP) Scam Only Works on a PC
URGENT ACTION: Critical WSUS Flaw (CVE-2025-59287) Actively Exploited (CVSS 9.8). Patch Now!
The ClickFix Attack: How “Copy & Paste” Leads to Remote Code Execution (RCE)
UFW Limit: The Smart Defense Against Brute-Force Attacks
How to Scan for Rootkits and Malware on Linux Servers with chkrootkit

Juliana Mascarenhas
Data Scientist and Master in Computer Modeling by LNCC.
Computer Engineer
Zabbix FIM: How to Setup File Integrity Monitoring
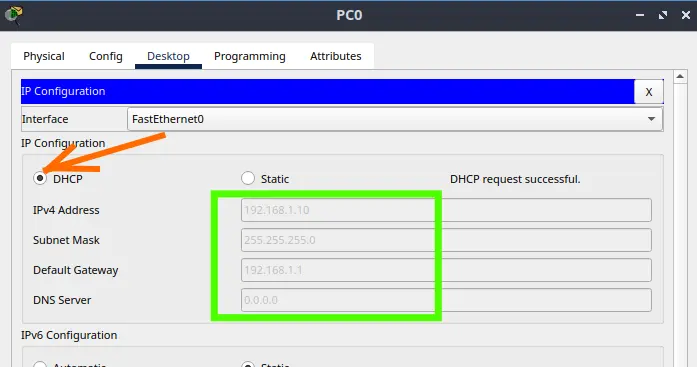
Configure DHCP in Packet Tracer: Server & Router Guide
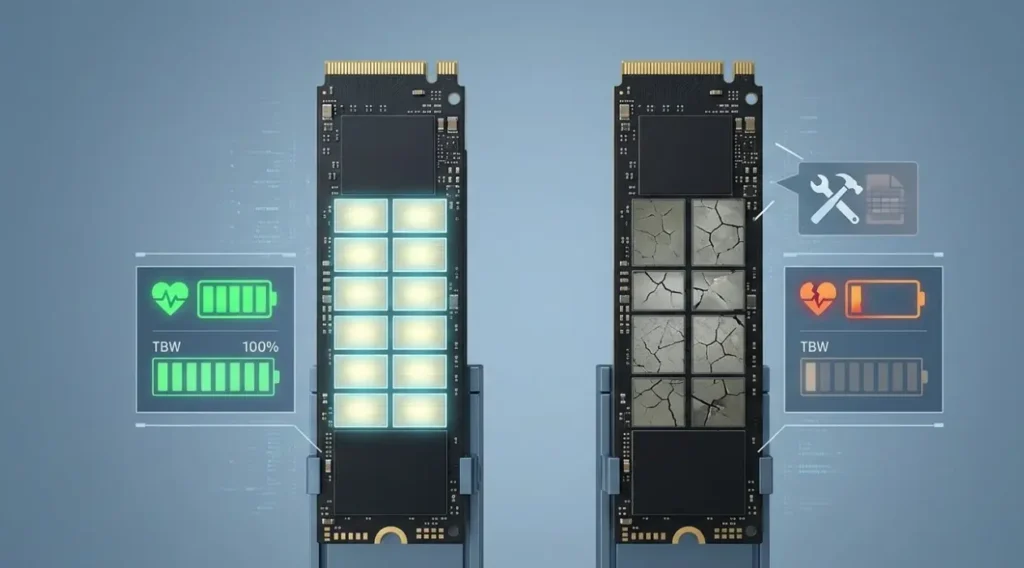
Cheap SSDs: The Hidden Dangers of TLC, QLC & DRAM-less
Zabbix Tags Guide: Organizing and Filtering Monitoring Alerts
If you manage a Zabbix environment, you’ve probably been there: a crowded “Problems” screen, where…
Flooding Routing Algorithm: How It Works & Use Cases
Let’s talk about one of the most primitive and, at the same time, most robust…
Routing & Dijkstra’s Algorithm: Finding the Internet’s Shortest Path
If you have ever used a GPS to avoid traffic, you already intuitively understand the…