Let’s talk about one of the most primitive and, at the same time, most robust routing techniques: Flooding.
Imagine you need to spread urgent gossip. You don’t choose a specific person; you shout to everyone nearby, and those people shout to the next ones, and so on. That is Flooding.
1. How does it work in practice?
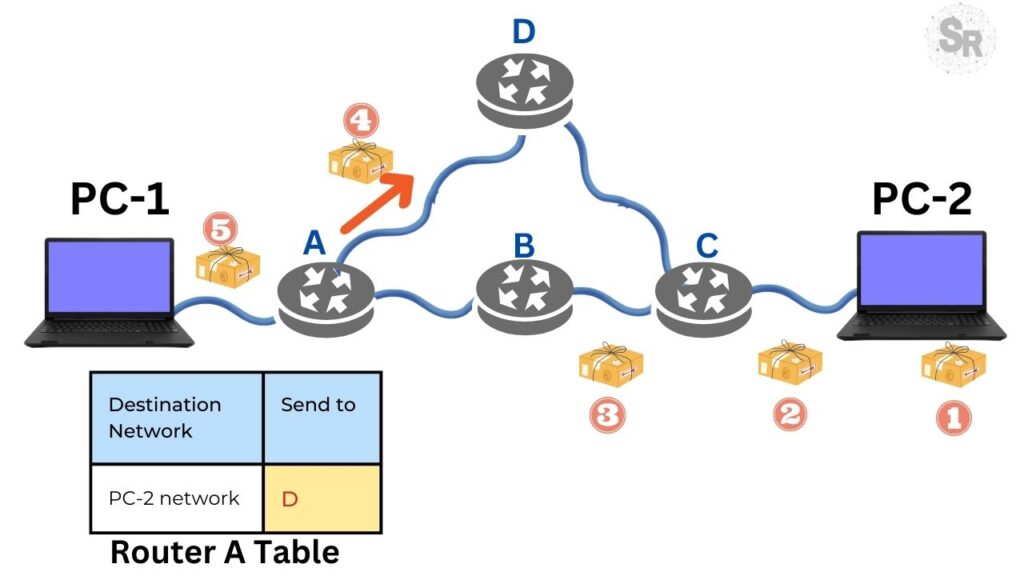
When a router implements Flooding, the rule is simple and does not require global network intelligence:

Golden Rule: Every packet arriving on a port is forwarded instantly to all other output ports, except the one it arrived on.
2. The Problem: The Packet Storm
If we let this process run loose, we create chaos. Imagine a packet running in circles infinitely.
This would generate an infinite amount of duplicate packets, crashing the network. To avoid this disaster, we need “brakes”:

- The Hop Counter: It’s like an “expiration date” in the packet header. If we define that the packet can make 10 hops, at each router it passes, we decrease 1. Reached zero? The packet is discarded. Generally, we use the network diameter (the longest possible path) as the initial value.
- Tracking Control (Sequence Number): A smarter technique. The source router marks each packet with a unique ID. The other routers keep a list (“Have I seen packet #50 from Source X?”). If the router has seen that packet before, it discards it and does not flood the network again.
- Optimization tip: So the list doesn’t get huge in memory, a counter $k$ is used. The router assumes: “I’ve seen everything that came before number $k$”.

3. If it’s so “brute”, why do we use it?
In everyday life, to load a web page, Flooding is terrible (it generates a lot of garbage/useless traffic). But it has specific superpowers:
- Extreme Robustness (War Mode): Imagine a military network where routers are being destroyed. If there is at least one physical path between the source and the destination, Flooding will find it, because it tries all possible paths simultaneously.
- Zero Configuration: The router only needs to know who its direct neighbors are. No complex tables.
- Wireless Networks: Wi-Fi already works naturally like this. When you transmit, everyone in radio range receives the signal.
- The “Gold Standard” for Comparison: Since Flooding traverses all paths in parallel, it will always find the shortest path possible. No other algorithm can deliver a packet faster than it (ignoring the congestion it creates itself). That’s why we use Flooding as a basis to measure the efficiency of other more complex algorithms.
Conclusion on Flooding routing
Flooding is inefficient for common traffic because it duplicates data too much, but it is unbeatable when we need to ensure that a message reaches everyone (broadcast) or when the network is very unstable and we need guaranteed delivery at any cost.
See more:
Routing & Dijkstra’s Algorithm: Finding the Internet’s Shortest Path
Congestion Control in Networks: Optimizing Efficiency and Bandwidth Allocation
https://www.cisco.com/c/en/us/support/docs/switches/catalyst-6000-series-switches/23563-143.html

Juliana Mascarenhas
Data Scientist and Master in Computer Modeling by LNCC.
Computer Engineer
Zabbix FIM: How to Setup File Integrity Monitoring
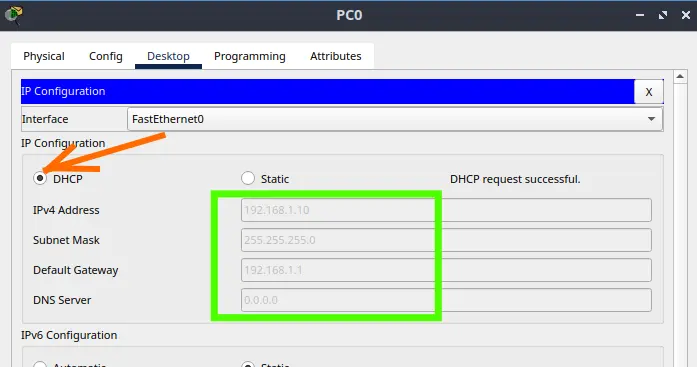
Configure DHCP in Packet Tracer: Server & Router Guide
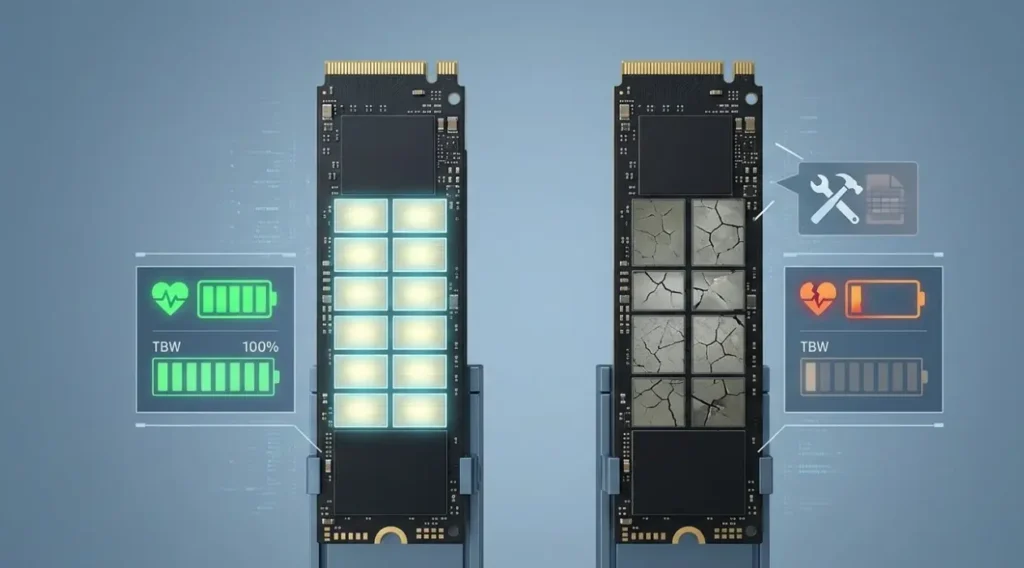
Cheap SSDs: The Hidden Dangers of TLC, QLC & DRAM-less
Zabbix Tags Guide: Organizing and Filtering Monitoring Alerts
If you manage a Zabbix environment, you’ve probably been there: a crowded “Problems” screen, where…
Flooding Routing Algorithm: How It Works & Use Cases
Let’s talk about one of the most primitive and, at the same time, most robust…
Routing & Dijkstra’s Algorithm: Finding the Internet’s Shortest Path
If you have ever used a GPS to avoid traffic, you already intuitively understand the…