In recent weeks, this new banking trojan (malware focused on stealing bank data) has exploded in the country. Reports from companies like Kaspersky indicate tens of thousands of infection attempts, all starting the same way: a simple message on WhatsApp.
The message, often coming from a known contact, contains a .ZIP file and a curious instruction: “Viewing allowed only on computers.”
This raises the central question I’ve been receiving: If the scam arrives on my phone, why does it need my computer to work?
The answer reveals the anatomy of a modern attack and the crucial difference between the security architecture of a smartphone and that of a PC. Let’s dissect this malware.
The Golden Question: Why the PC and not the Phone?
The short answer is: the malware was not made for your phone.
Think of your phone (Android or iOS) as a fortress with maximum-security cells. The malware (the .ZIP file and the .LNK shortcut inside it) is like a prisoner who speaks a foreign language and doesn’t even have the tools to try to open the cell door.

Your phone’s system simply ignores the malicious file for two main reasons:
1. The Phone’s Security “Cage” (Sandboxing)
This is the most important concept. On your smartphone, every app lives in its own “sandbox,” completely isolated from the others.
- WhatsApp does not have permission to read what happens in your Banking App.
- Your Banking App cannot see what you do in your Browser.
The malware, upon arriving in WhatsApp, is trapped inside the WhatsApp “sandbox.” It cannot spy on other apps. Furthermore, the phone doesn’t know what to do with a “Windows Shortcut” file (.LNK). It’s the wrong tool for the job.
2. The Malware was “Built” for Windows
The PC, on the other hand, is a much more open and complex environment. Maverick was designed specifically to exploit tools that only exist in the Windows operating system:

- The Shortcut (
.LNK): This is the “trigger” the user clicks. - The
cmd.exe: The classic Windows command prompt, used as a bridge. - The
PowerShell.exe: The secret weapon. This is a powerful, native Windows administration tool that the malware uses to download and execute its components directly in RAM. - The
.NET Framework: The Microsoft software platform on which the actual banking trojan was programmed.
None of these components exist on your phone. The attack was architected from scratch for the Windows ecosystem, where it can monitor the keyboard, browser, and user activities with much more freedom.
The Maverick Lifecycle: The Attack Chain Visualized
In our field, to understand a threat, we “draw” it. I’ve created a flow diagram that shows exactly how Maverick moves, from delivery to data theft and its propagation.

Let’s analyze the flow:
- Phase 1: Distribution (The Vector) It all starts with a previously infected victim. The malware on their PC uses their active WhatsApp Web session to automatically send the message with the
.ZIPfile to their contacts. The social engineering (“Open on PC”) ensures the victim moves to the right target. - Phase 2: Execution (The PC Host) The victim, now on their computer, opens the
.ZIPand clicks the.LNKshortcut. This click is the “trigger” that initiates the attack. - Phase 3: “Fileless” Infection (In-Memory) Here is the cleverest part of the attack. The
.LNKcallscmd.exe, which in turn executesPowerShell. PowerShell connects to the criminal’s server (C2) and downloads the main malware (a.NETcomponent) directly into RAM.This is called a “Fileless” attack, as nothing is saved to the hard drive. Many traditional antiviruses, which look for malicious files on the disk, are “blinded” by this technique. - Phase 4: Action on Target (The Theft) Once in memory, the Maverick “wakes up.” It first checks if it is in Brazil (checks time zone and language). If so, it starts monitoring the user, waiting for them to access banking or cryptocurrency exchange sites. It then steals credentials using keylogging (recording what is typed) and capturing the screen.
- Phase 5: Propagation (Restarting the Cycle) To close the loop, the malware detects the new victim’s WhatsApp Web session and repeats Phase 1, spreading to even more people.
How to Protect Yourself from Maverick
The good news is that, although sophisticated, Maverick relies entirely on an initial human error. Knowledge is your best defense.
- Be Wary of
.ZIPFiles on WhatsApp: Companies rarely send quotes or receipts via WhatsApp in this way. - The
.LNKRule: NEVER click on a Shortcut (.LNK) file that came from an email or message. Shortcuts are for opening programs on your own PC, not for viewing documents. - The “Open on PC” Alert: If a WhatsApp message asks you to switch to a computer to view a file, be 99.9% suspicious. It is a strong indicator of a scam.
- Disconnect WhatsApp Web: If you suspect you have been infected, go to your phone, open WhatsApp > Settings > Linked Devices, and disconnect all active sessions.
- Keep Your System Updated: Have a good antivirus/EDR (Endpoint Detection and Response) solution and always keep Windows and your browser updated.
Maverick is a clear reminder that cybersecurity is a cat-and-mouse game. The criminals have adapted their attack perfectly, using the phone as bait and the PC as the final target.
Stay vigilant.
See more:
https://www.broadcom.com/support/security-center/protection-bulletin/maverick-banking-trojan

Juliana Mascarenhas
Data Scientist and Master in Computer Modeling by LNCC.
Computer Engineer
How to Configure NAT in Packet Tracer (Step-by-Step)
Zabbix FIM: How to Setup File Integrity Monitoring
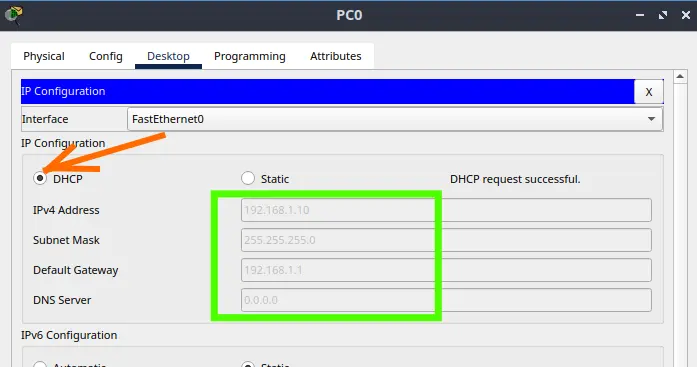
Configure DHCP in Packet Tracer: Server & Router Guide
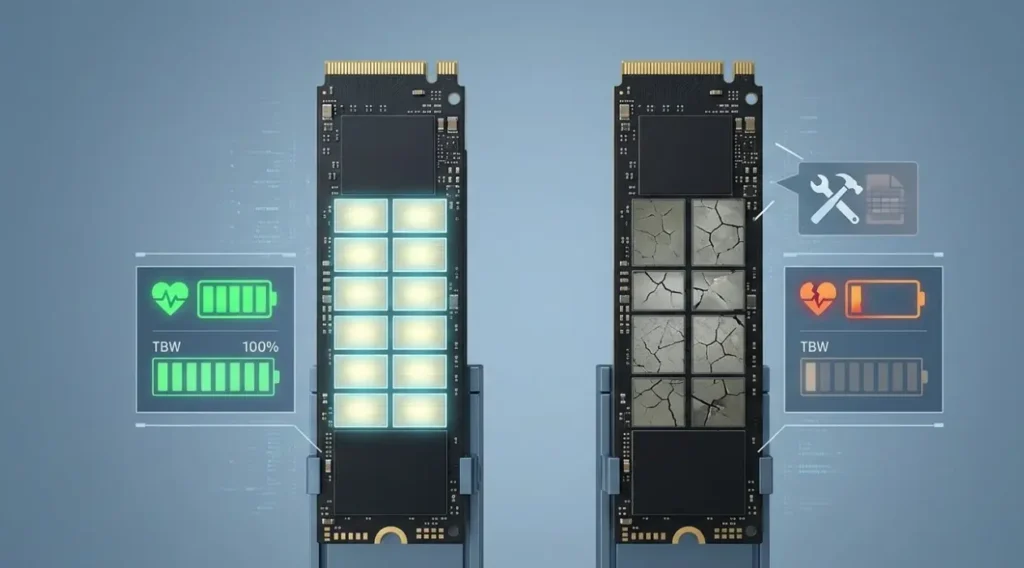
Cheap SSDs: The Hidden Dangers of TLC, QLC & DRAM-less
Zabbix Tags Guide: Organizing and Filtering Monitoring Alerts
If you manage a Zabbix environment, you’ve probably been there: a crowded “Problems” screen, where…
Flooding Routing Algorithm: How It Works & Use Cases
Let’s talk about one of the most primitive and, at the same time, most robust…