Text documents are extremely common attack vectors. Often, we receive a file that seems harmless but can hide malicious scripts (macros) or phishing links.
In this tutorial, I will show how I performed a forensic analysis on an .odt (LibreOffice) file using only the Linux terminal.
We will discover if the file has hidden macros, check metadata, and extract links without needing to open the document. This will increase analyst security.
The tools we will use are: ExifTool, Unzip and Grep.
Step 1: Initial Reconnaissance with ExifTool
The first step of any forensic analysis is understanding the file’s origin without executing it. The exiftool command is perfect for reading metadata.
In this case, we are investigating the file Untitled 1.odt.
I used the -v (verbose) flag to try to see not only the basic data but also the internal XML structure.
The Command:
exiftool -v "Untitled 1.odt"
The Result: Here we can see valuable information, such as the generator software (LibreOffice 24.2) and the operating system (Linux X86_64), which helps create a profile of the file’s origin.
Actual analysis output:
FileModifyDate = 1765105816
FileType = ODT
MIMEType = application/vnd.oasis.opendocument.text
Generator = LibreOffice/24.2.7.2$Linux_X86_64 LibreOffice_project/420$Build-2
...Step 2: Hunting for Macros (The File Structure)
Many analysts forget that .odt files (just like .docx) are actually compressed (ZIP) files. This means we can list their contents without opening the text editor.
For an ODT file to have a macro (malicious executable code), it must have a folder named Basic/ or Scripts/ in its structure.
Let’s check this with unzip:
The Command:
unzip -l "Untitled 1.odt"Result Analysis: In the file I analyzed, the output listed images and configuration XMLs, but no script folder.

Verification log:
Archive: Untitled 1.odt
Length Date Time Name
--------- ---------- ----- ----
20672 2025-12-05 15:19 styles.xml
55869 2025-12-05 15:19 content.xml
29852 2025-12-05 15:19 Pictures/100000010000034100000189085A293B.png
...Verdict: The file is clean of code execution (Macros).
Step 3: Detecting Phishing (Link Extraction)
If there are no macros, the danger might lie in a malicious link. Warning: Never use the cat command on ODT files, as they are binaries and will mess up your terminal configuration.
The correct way is to use unzip -p (pipe) to read the content.xml file (where the text is located) and filter for links.
The Noisy Attempt (What not to do): If we just do a grep for “http”, we will have many false positives, because LibreOffice XML uses URLs to define its own standards (namespaces).
unzip -p "Untitled 1.odt" content.xml | grep -oP 'http[s]?://[^"]+'This returned dozens of lines from W3C and OpenOffice.org that are not clickable links.
The Surgical Approach (The right way): To find real phishing links, we must search for the xlink:href attribute, which is where the clickable link actually resides.
The Command:
unzip -p "Untitled 1.odt" content.xml | grep -oP 'xlink:href="\K[^"]+'
The result:
Pictures/10000001000000DB000001AFC762D0A7.png
Pictures/100000010000013D000000E64AE49725.png
Pictures/10000001000001E2000001624AEC2141.png
...Note that the “links” found point to the internal Pictures/ folder. This confirms that there are no external links to fake sites. The document contains only locally embedded images.
Analysis Conclusion
With just three commands in the terminal, we were able to determine that:
- The file was generated in a Linux environment.
- It has no executable code (Macros).
- It has no external phishing links.
This quick screening is essential for security professionals before opening any suspicious attachment in an isolated environment (sandbox).
See more:
5 Obsolete Kali Linux Tools and Their Modern Replacements
Maverick Malware: Why the WhatsApp (.ZIP) Scam Only Works on a PC
The ClickFix Attack: How “Copy & Paste” Leads to Remote Code Execution (RCE)
UFW Limit: The Smart Defense Against Brute-Force Attacks
How to Scan for Rootkits and Malware on Linux Servers with chkrootkit

Juliana Mascarenhas
Data Scientist and Master in Computer Modeling by LNCC.
Computer Engineer
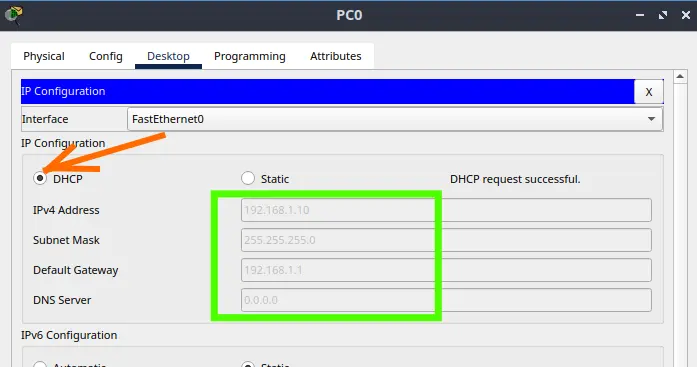
How to Configure NAT in Packet Tracer (Step-by-Step)
Zabbix FIM: How to Setup File Integrity Monitoring
Configure DHCP in Packet Tracer: Server & Router Guide
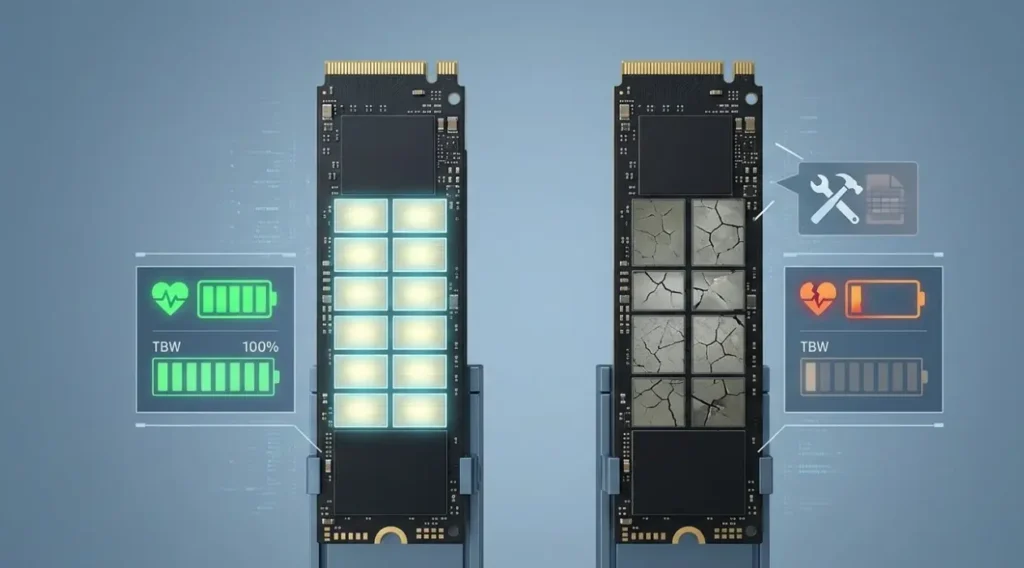
Cheap SSDs: The Hidden Dangers of TLC, QLC & DRAM-less
Zabbix Tags Guide: Organizing and Filtering Monitoring Alerts
If you manage a Zabbix environment, you’ve probably been there: a crowded “Problems” screen, where…
Flooding Routing Algorithm: How It Works & Use Cases
Let’s talk about one of the most primitive and, at the same time, most robust…