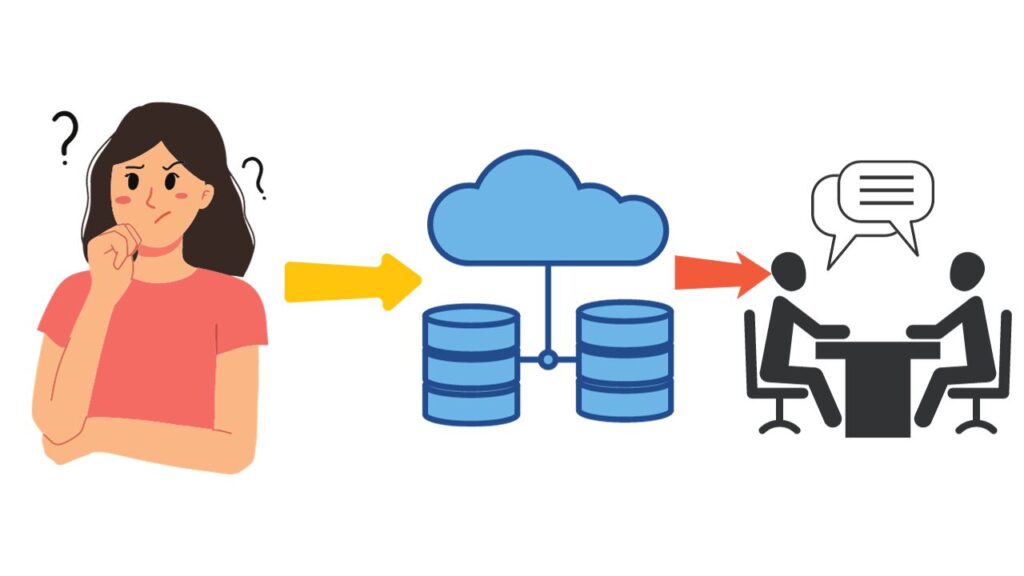
You are hired to model a client’s database system. And now? What do you need to do?
In this scenario, the client needs you to understand the context of their business so that it can be transformed into a relational model.
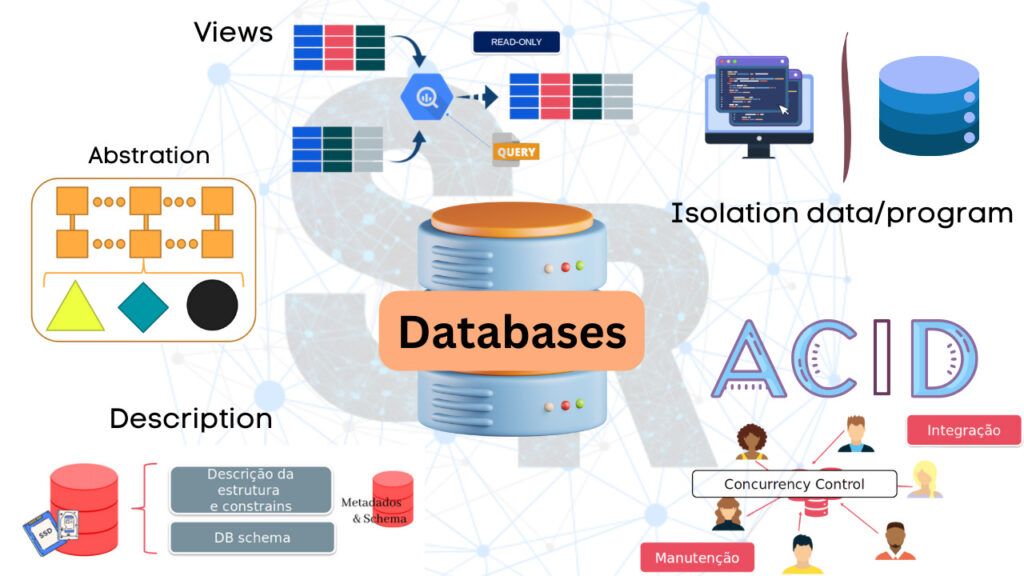
OK… within a database project we already have the steps well defined. We create a high-level version of an ER schema – Entity Relationship – and then transform it into a relational schema.
If we are sure that it is a relational database model, we can go directly to the relational schema. But we have a gap here…
How to deal with the customer?
All of this is still very technical for the customer. Even if you use an ER schema, depending on the scope that makes up the mini-world, it will still be difficult for your client to understand what you are doing.
So what do you do in a situation like this? I can list some aspects that deserve attention:
1. We need to define business rules. Understand what your customer’s world is about. This way you will probably make better modeling decisions.
2. Set the depth level of the information. Knowing what needs to be mapped will make your database more effective.
3. Hold meetings with your client to align expectations and answer questions about the business. This will save you time with rework
4. Don’t assume anything, ask. No matter how obvious an element may seem, confirm with your client. It may be that he has a different understanding than you.
5. Formulate questions. Define together with your client what they expect information to be returned. This way, you’ll know if you modeled the mini-world correctly.
6. Document! Yes, document the entire process. You will have contact with a lot of information and you won’t remember everything. Use documentation as your ally.
Well… I hope these tips help you approach your client. So, what other method do you use to improve your communication with your customers?
These were some thoughts on the subject, if you want to know more about it you can send questions on Linkedin!
See you next time!
More database posts
Where to Start in the Data Science Career?

Juliana Mascarenhas
Data Scientist and Master in Computer Modeling by LNCC.
Computer Engineer
How to Configure NAT in Packet Tracer (Step-by-Step)
Zabbix FIM: How to Setup File Integrity Monitoring
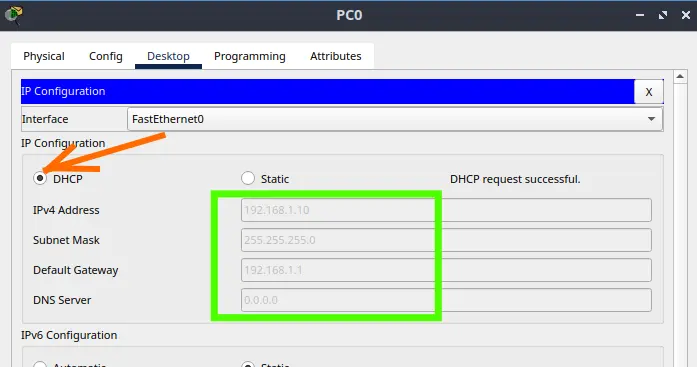
Configure DHCP in Packet Tracer: Server & Router Guide
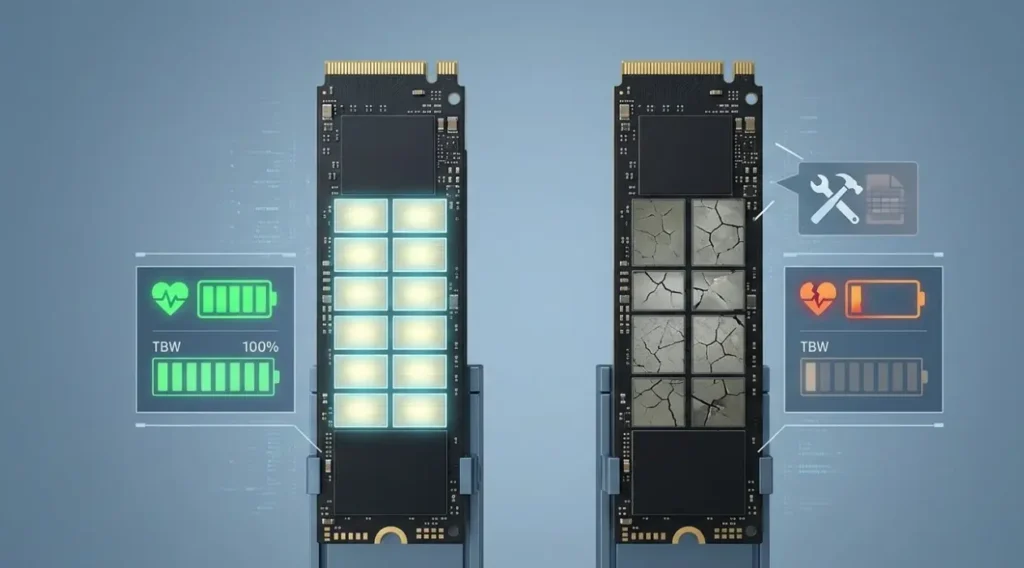
Cheap SSDs: The Hidden Dangers of TLC, QLC & DRAM-less
Zabbix Tags Guide: Organizing and Filtering Monitoring Alerts
If you manage a Zabbix environment, you’ve probably been there: a crowded “Problems” screen, where…
Flooding Routing Algorithm: How It Works & Use Cases
Let’s talk about one of the most primitive and, at the same time, most robust…